The primary difference between Cardano and Ethereum lies in their ledger models and development philosophies. Cardano adopts the Extended UTXO (EUTXO) model derived from Bitcoin and emphasizes formal verification and academic rigor. Ethereum, by contrast, uses an account-based model and, as a pioneer of smart contracts, prioritizes rapid ecosystem iteration and broad compatibility.
2026-03-24 22:08:29
Security researchers have identified that hackers are exploiting "search poisoning" to manipulate Bing AI search results, steering users toward downloading a fake OpenClaw application embedded with infostealer malware, leading to the theft of crypto assets and sensitive information. This article examines the attack methodology, technical specifics, and the broader implications for the industry.
2026-03-24 18:49:16
A user on CoW Swap exchanged roughly $50.43 million in aEthUSDT for AAVE. Because slippage exceeded 99%, the user ended up with only about $36,000 in assets, sparking widespread market concern. This article examines Aave's collateral swap mechanism, transaction routing challenges, and associated DeFi risks.
2026-03-24 15:22:14
Resolv's USR stablecoin experienced a significant security breach, allowing an attacker to mint 80 million uncollateralized tokens and liquidate roughly $25 million, which caused a substantial price depeg. This article offers an in-depth examination of the incident, the attack method, and the inherent risks of DeFi stablecoins.
2026-03-24 11:58:51
Multisignature (multisig) technology has greatly improved the security and flexibility of cryptocurrency storage. By eliminating the single point of failure associated with private keys, it lays a strong foundation for asset management, enterprise applications, and innovative financial services. However, like any complex system, multisig can also become a target for attackers, and scams involving it are becoming increasingly common. This article explores the advantages and risks of multisig solutions and provides practical safety tips to help users fully leverage the benefits of multisig wallets while minimizing potential threats.
2026-03-24 11:56:56
Gate Research: In March 2025, the Web3 industry experienced eight security incidents, resulting in total losses of $14.43 million—a significant decrease compared to the previous month. The majority of attacks involved smart contract vulnerabilities and account compromises, accounting for 62.5% of all crypto-related incidents during the period. Major cases included a $5 million exploit targeting 1inch (with 90% of the stolen funds recovered) and two separate attacks on Zoth involving a contract flaw and a private key leakage, leading to combined losses of $8.575 million. In terms of blockchain distribution, only one project this month reported losses on the public blockchain BSC.
2026-03-24 11:56:55
This article will provide a detailed discussion on various aspects, including the current state of Web3 security threats, self-custody of personal assets, device and network environment, zero-trust strategy, and global security incident statistics. It aims to offer an effective Web3 security prevention guide for industry professionals and investors.
2026-03-24 11:56:54
The Nakamoto Coefficient is a critical metric for assessing the decentralization level of a blockchain. Learn about its definition, calculation method, influencing factors, and its role in blockchain security and governance to ensure network stability and fairness.
2026-03-24 11:56:53
In the realm of digital assets, security protection is crucial. This article provides systematic security recommendations focusing on seven key areas: account security, device protection, phishing attack identification, data encryption, payment safety, on-chain privacy protection, and personal information management. Real-world cases are analyzed to reveal potential security risks and corresponding countermeasures. In the future, exchanges must adopt more cutting-edge technologies, such as artificial intelligence and blockchain analytics, to enhance their security capabilities.
2026-03-24 11:56:50
This article explores why NFT holders have become prime targets for hackers, analyzing common NFT theft tactics such as sudden increases in wallet assets. Through real-world cases, we’ll uncover the hidden threats of NFT scams and provide practical security tips to help you protect your assets and boost wallet security.
2026-03-24 11:56:50
Through data and case analysis, this article reveals how sandwich attacks have evolved from "guerrilla warfare" to "assembly line harvesting," and how the distortion of the priority fee mechanism exacerbates user burdens and trust crises.
2026-03-24 11:56:49
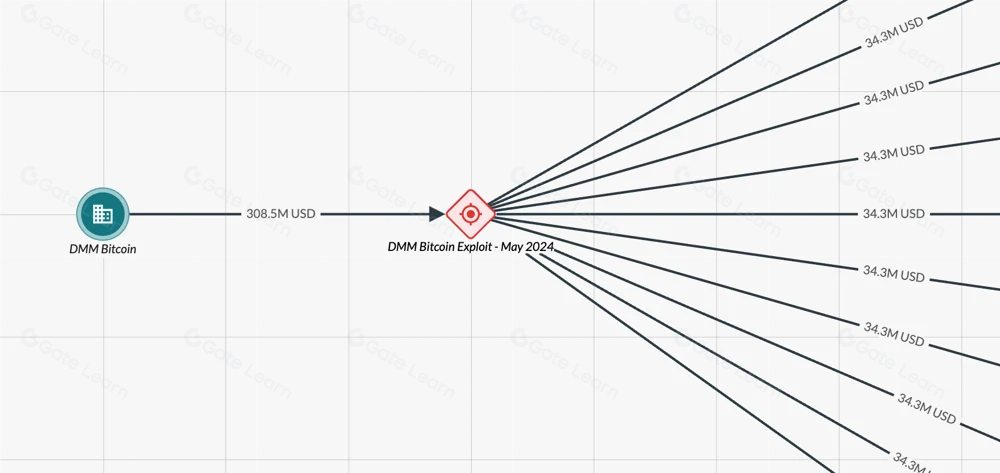
This research delves into the current state of hacking attacks and presents a detailed analysis of their multifaceted impact on the crypto market, based on several major cryptocurrency hacking incidents. The analysis examines both direct and indirect effects, including market volatility and changes in investor behavior. The research highlights potential risks that the crypto market faces and explores possible strategies for mitigating these risks in the future.
2026-03-24 11:56:49
This article explores the role of cryptocurrency as evidence in criminal cases, its classification as illegal gains, and how it is treated before and after court rulings. It highlights that while cryptocurrencies are widely acknowledged in legal contexts as having monetary value, there are still numerous legal and practical challenges in their management.
2026-03-24 11:56:48
Remote work scams in the cryptocurrency industry are on the rise. Scammers pose as legitimate companies on social platforms, luring job seekers with promises of high-paying remote positions to steal their money and personal data. They employ various tactics—charging training fees, marketing fraudulent training programs, and tricking victims into downloading malware. High-profile cases like GrassCall and CrowdStrike show how these criminals use phishing and malware attacks to steal crypto assets. To stay safe, job seekers must watch for warning signs like upfront payment demands, rushed hiring processes, and unverified company credentials.
2026-03-24 11:56:46
This article introduces the concept of Regenerative Finance (ReFi), its market potential, application scenarios, operational mechanisms, and noteworthy projects. It also compares ReFi with DeFi, exploring its future development trends and potential risks.
2026-03-24 11:56:46